Hacker Generations and Evolution
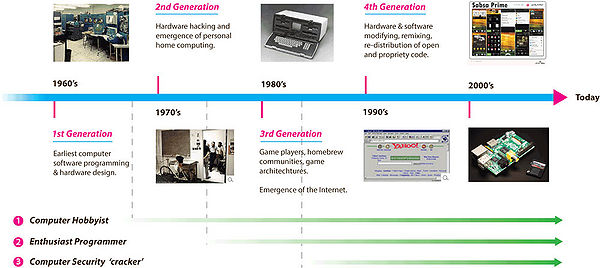
Although the extant typology of hacker activities along the illegal-to-legal dimension is useful in delineating differing types in terms of destructivity, creativity, piracy and theft, remixing of value etc., it does not take into account the evolution of different hacker types over time since their initial emergence. The typology assumes all hackers are constituent of the same generation, which is clearly not the case, given the incremental emergence of hacker generations since the 1960’s (see below).
Viewed in this way in temporal form, the Computer Security Crackers are a relatively new phenomenon; an inevitable result by those seeking to exploit and illegally profit from new emergent and openly available technologies (distributed home computing, micro-chips, networks and Internet communication technologies).
Computer Hobbyists and Enthusiast Programmers emerged long before Computer Security Crackers (despite the current focus of meaning in popular culture) and in some instances created entire industries as in the personal home computing sector.
Hackers were in fact first defined in 1984 in a book called Hackers: Heroes of the Computer Revolution, described as having evolved through several generations. An extension of this is offered below.
Contents
1st Generation Hackers (1960’s/70’s)
- Hackers involved in the earliest computer programming techniques development for technology exploration.
2nd Generation Hackers (mid 1970’s to mid 1980’s)
- Hackers in computer hardware production during the advent of Personal Computer by modifying and creating new hardware configurations (Apple, Microsoft: Jobs, Wozniak, Allen, Gates et al.).
3rd Generation Hackers (1980’s to mid 1990’s)
- Hacker-game players devoting leisure time to writing scripts and programmes for game architectures amidst the emergence of Open Source software development [Jeppessen, 2003].
4th Generation Hackers (late 1990’s to today)
- Hackers freely modifying, remixing, reconfiguring and re- distributing open and proprietary knowledge extracted from creative IP from consumer artefacts, technology, products and services facilitated by the use of information and communication technologies (ICT’s).
There is a significant need to understand the true meaning of hacking, not from a sensationalist media perspective but from its origins to uncover its motivation, goals and aims; and to find exactly what role hacking plays in today’s digitally networked society. Media coverage of hacking does nothing to promote scholarly attention to the understanding of the wider role hacking plays, and merely demotes it to illegal deviant activities involving crime, dark sub-cultures with gang mentalities. In some contexts along the illegal-to-legal dimension, these perceptions are entirely valid, but they do not hold for all types of hacking activity that can represent generativity, creativity and problem solving solutions. Only by broadening our understanding of hacking can we begin to see other forms of hacking that are not simply negative and destructive but are creative sources of potential innovation by hacker-innovators and end users alike that can be a significantly beneficial source for organisations seeking to create better experiences, products and services for their consumers.
Re-framing the extant hacker typology
Common to all forms hacking activity along the illegal-to-legal dimension, are set of cultural beliefs and values that can shed light on motivations for the initiation of a hack in the first place. The table below shows a summary of the three main hacker activity types and the degree to which such acts may be deemed illegal by institutions or organisations claiming private intellectual property ownership over artefacts.
 Typology of hacker classes along legal to illegal/closed to open dimensions.
Typology of hacker classes along legal to illegal/closed to open dimensions.
As discussed so far, illegal and negatively perceived activities (in a non-market value generation sense) form only part of overall hacking landscape, despite being those that predominate in the popular media and resulting cultural consciousness. Other forms of hacking clearly do exist, albeit perhaps to lesser degrees of illegality in combination with some market value generating potential.
Analysing hacker activities along a negative (destructive-illegal) to positive (generative-legal) dimension allows us to break away from the stereotypical, popular cultural understanding of hacking by expanding our moral and ethical boundaries outside the stereotypical notions of deviant, criminal acts. Once this is understood, other, possibly illegal but generative and perhaps useful forms of hacking can be discussed and explored. This is highly important as firms should not simply, automatically and instinctively condone, disregard, legislate against and prosecute forms of hacking by users as a threat to firm interests, at least not in all hacking cases. Instead, a deeper understanding is needed to seek-out potential commercial uses for such activities, by engaging with or even encouraging hacker activities in order to gain knowledge that would not otherwise be generated by standard internal research and development processes. Firms that can leverage this typically unrealised source of innovation will gain a vital source of complimentary knowledge. This could be used to help future product design and development generations, inform upon industry and product class design trajectories, as well as help build open modularity into complex systems and promote social innovation development where desired. Much of this could help firms gain additional unrealised competitive advantage over those firms with a typically closed market strategy and sole internal R&D by leveraging activities within forms of hacker innovation.
If considered in this wider sense, hacking can be framed as a communal pool of expert knowledge and skills applied with passionate-inquisitiveness to an existing technological artefact as a source of innovation or value generation, whether for the general market or personal consumption.[1] Outcomes as to the usefulness of overall hacker innovation activities are dependent upon a number of institutional factors, political motivations, firm interests, desires, morals and ethics.
In a broader contextual framing, destructive criminal hacking acts form only a small proportion of the overall activities undertaken in the unconstructive, non- generative sense, particularly for innovating organisations. There is however an academically under-researched area of innovation (between script kiddies and end-user innovators) that lies beyond the market usefulness boundary, known as the hacker-innovator class (see diagram below).
 The illegal-to-legal dimension: degrees of legality and openness with potential market usefulness through hacker activities.
The illegal-to-legal dimension: degrees of legality and openness with potential market usefulness through hacker activities.
The market usefulness boundary generally delineates the point at which a potential source of innovation begins to emerge and could prove useful to firms engaged in the development management of their product innovation classes. Exploiting an innovation source such as this should have the potential enable the link between producers and consumers to be tighter by improving the performance, quality, features and other consumer value metrics, used for reducing uncertainty in the innovation process of future product class generations.
Footnotes
- ↑ Instead of simply stealing data or breaking into computer systems in the Computer Security Cracker sense.
References
- [Jeppessen, 2003] ^ Jeppessen, L. B. M., M. (2003). "Consumers as Co-Developers: Learning and Innovation Outside the Firm." Technology Analysis & Strategic Management 15(3).